- BEAD compliance is a vendor coordination problem, not just a data problem. Most providers are assembling compliance across engineering firms, software providers, and IT partners, each owning a piece of the picture and none owning the outcome.
- When data does not align across vendors, the result is finger-pointing, delays, and providers left in the middle trying to reconcile conflicting information.
- CHR Solutions eliminates that risk entirely. We are the single partner that provides engineering, operations, and customer data: one relationship, one accountable team, no gaps.
- Providers who consolidate with a single partner now will avoid the compliance failures that fragmented vendor relationships make nearly inevitable.
BEAD Compliance Is Proving More Complex Than Expected
What does BEAD compliance require from broadband providers?
As providers work through BEAD requirements, one pattern is becoming clear: this is more than a reporting exercise. What looks like a checklist is forcing visibility into how data moves across an entire organization, and often across multiple vendors that were never designed to work together.
BEAD compliance requires providers to maintain a continuous, documented record of every location from planning through construction, service activation, and beyond. Speed and latency thresholds must be proven with audit-ready data, not just advertised. Milestone dates must be captured at the time of construction. Pricing history must be retrievable and defensible over a multi-year period.
Is BEAD compliance a one-time reporting effort?
No. BEAD is not a final step that happens after construction. It must be built into how operations run from the start. Reporting is ongoing, multi-year, and tied to continued funding eligibility. The assumption that compliance follows construction, build the network, turn up service, then generate the reports, does not hold. Providers who treat it that way will face data gaps they cannot close after the fact.
For providers managing that process across engineering firms, software vendors, and IT partners, the coordination challenge alone creates significant risk.
The Vendor Problem Nobody Is Talking About
Why do most broadband providers already have the data BEAD requires?
Most providers are not struggling because they lack data. They are struggling because that data lives across multiple vendors, each responsible for a different piece of the compliance puzzle:
- Engineering firms track builds, milestones, and construction timelines.
- Software providers manage billing, customer records, and service activation.
- IT partners handle network performance, monitoring, and infrastructure.
In most cases, yes, the data exists. The challenge is that it is fragmented across systems. BEAD requires a single, connected view across all of it: from when a location is planned through to when a customer is activated and beyond. When that view does not exist, providers end up manually pulling data from multiple sources and hoping it aligns.
What happens when vendor data does not align for BEAD reporting?
It rarely does. When it does not, every vendor points to another. That is a structural problem, not a data problem, and it will not resolve itself as reporting requirements scale. Every disagreement over data ownership becomes a delay. Every finger pointed at another vendor is time and cost the provider absorbs.
Where the Checklist Is Exposing Real Gaps
The BEAD checklist itself is straightforward. The challenge is what sits behind it. Each compliance requirement connects to a different system, a different team, and often a different vendor. Here are the questions providers are asking most often, and where the gaps are appearing.
What happens if milestone data is not tracked early in construction?
It cannot be recreated later. BEAD requires documented proof of when construction milestones were completed, and that record must exist at the time the work happens. Providers who rely on engineering firms to track builds and then try to pull that data together later for compliance reporting, consistently find the information incomplete, inconsistent, or formatted in ways that do not match what other vendors are holding. When no single partner owns the full build record, there is no single source of truth to report from.
How do providers prove network performance meets BEAD thresholds?
Performance data must be continuous, audit-ready, and tied to specific locations, not just advertised speeds. Providers cannot select their best-performing locations for the report. BEAD requires defensible data across the full-service area, measured consistently over time. When a separate IT partner manages performance monitoring, assembling that data for compliance reporting becomes a manual process that depends on vendor cooperation, not internal control. The further that data sits from the billing and engineering record, the harder it is to produce on demand.
How do providers document pricing history for BEAD audits?
Historical pricing data must be retrievable and be able to be validated over the life of the funded network. When billing systems and engineering records are managed separately, validating that history requires both vendors to align on what was charged, when, and to which locations. That alignment rarely happens cleanly. When auditors ask, the gap between what the billing system shows and what the engineering record reflects becomes a compliance problem with no quick fix.
How does BEAD compliance work across fiber, fixed wireless, and legacy platforms?
Each technology produces data differently. Fiber deployments, fixed wireless installations, and legacy platform upgrades generate different milestone records, different performance metrics, and different activation workflows. When different vendors manage different platforms, those formats do not naturally align. Providers working across multiple technologies face a compounding problem: the compliance expectation is uniform, but the underlying data is not. Without a single partner managing all of it, producing a consistent compliance record requires translation work that introduces both delay and error.
The Real Risk: Fragmentation Without Accountability
Why is lifecycle tracking so important for BEAD compliance?
BEAD reporting requires a complete history of a location, not just current service status. When different vendors own different parts of that lifecycle, the history is fragmented. Providers are not missing data; they are missing alignment. In most cases, that misalignment is not internal. It is the result of managing compliance across vendors.
This creates a specific, compounding risk. As reporting requirements scale, every gap in the vendor relationship becomes a gap in compliance. The providers in the strongest position will not necessarily be those with the most data. They will be the ones with a single partner accountable for all of it.
How CHR Solutions Closes the Gap
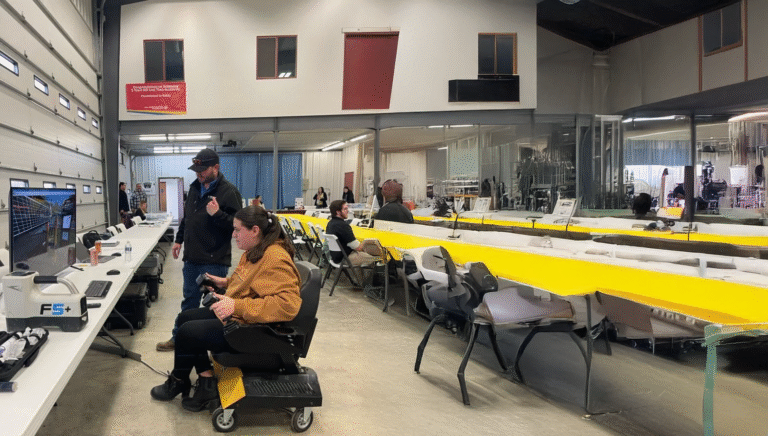
What if we are already working with multiple vendors for engineering, software, and IT?
That is exactly where risk compounds. Each vendor owns a piece of the data, but none owns the outcome. Most providers trying to solve BEAD compliance add coordination: more meetings, more integrations, more manual reconciliation across vendors. CHR Solutions takes a different approach.
We are the single partner that provides engineering, operations, and customer data. We do not integrate with your existing vendors. We replace the need for multiple vendors in the first place. One relationship. One team. One accountable partner across the full lifecycle of your network.
What That Means for Your BEAD Compliance
- No vendor finger-pointing: one partner owns the data, the process, and the outcome.
- Less manual reporting: data is aligned from the start, not assembled after the fact.
- Defensible, consistent data: reporting that holds up under scrutiny because it was built to.
- Confidence as requirements scale: a platform and a partner designed for multi-year BEAD reporting.
BEAD Compliance FAQ
The following questions reflect what broadband providers are actively asking about BEAD compliance requirements. CHR Solutions addresses each of these directly through its single-partner model.
What is the biggest challenge in BEAD reporting?
Aligning data across systems and vendors so it can be consistently reported over time. The data problem is usually a vendor coordination problem in disguise. Providers who have the data but cannot reconcile it across vendors face the same compliance risk as providers who never captured it.
Do providers already have the data required for BEAD?
In most cases, yes. The challenge is that it is spread across multiple vendors. Engineering firms, software providers, and IT partners each hold a piece. Without a single partner owning the full lifecycle, assembling that data into a defensible compliance record requires manual effort, vendor cooperation, and time providers do not have when deadlines arrive.
What cybersecurity requirements does BEAD impose on subrecipients?
Subrecipients must have both a cybersecurity risk management plan aligned with the NIST Cybersecurity Framework and a separate cyber supply chain risk management plan. Both must be operational before funds are allocated. When cybersecurity is managed by a separate IT vendor, ensuring that documentation is current, complete, and audit-ready requires close coordination that many providers are not structured to deliver.
Is BEAD compliance a one-time reporting effort?
No. It requires ongoing, multi-year reporting with consistent data validation across the full period of performance. That is why a single, accountable partner matters more than a short-term fix. The compliance obligation does not end when construction ends. It continues through customer activation, performance monitoring, and annual reporting for the life of the funded network.